It is that time yet again... Happy Patching!
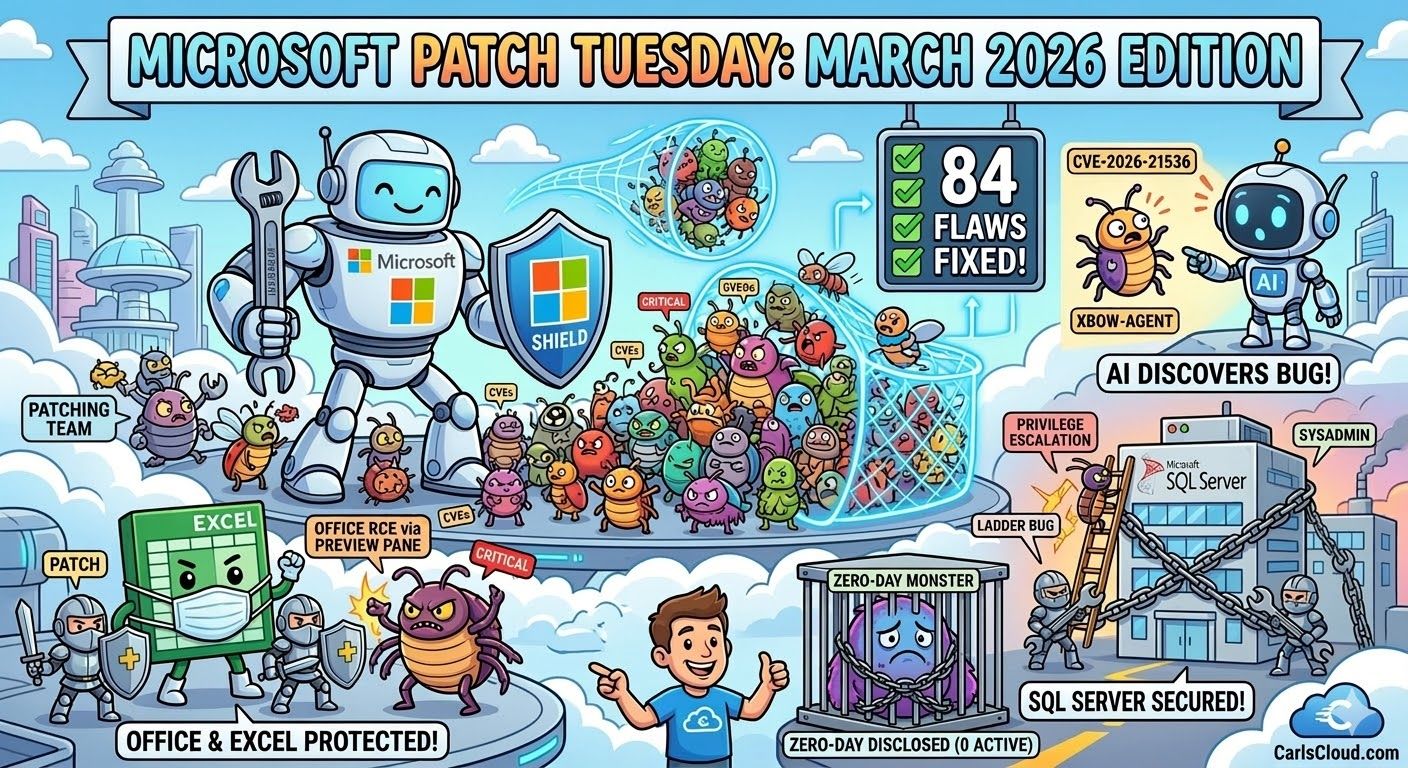
The March 2026 security update bonanza from Microsoft has arrived, and while we are spared from the high-pressure "zero-day" madness seen in February, there is plenty here that demands immediate attention.
This month, Microsoft addressed 84 security vulnerabilities across its ecosystem, including two publicly disclosed flaws and several critical issues affecting productivity tools like Office and SQL Server.
Whether you are a system administrator or a security-conscious user, this update highlights a significant shift in the threat landscape—specifically the rise of AI in vulnerability discovery.
Summary of March 2026 vulnerabilities at SANS

The Headlines: 84 Flaws and AI Discovery
Of the 84 CVEs patched this month, eight are rated as Critical and 76 as Important. The breakdown of vulnerability types is heavily weighted toward privilege escalation:
Elevation of Privilege: 46 vulnerabilities (55% of the total)
Remote Code Execution (RCE): 18 vulnerabilities
Information Disclosure: 10 vulnerabilities
Denial of Service: 4 vulnerabilities
Notably, this month features CVE-2026-21536, a critical RCE bug in the Microsoft Devices Pricing Program. While Microsoft has already mitigated this on the backend (requiring no user action), it is historically significant as one of the first vulnerabilities identified by an autonomous AI penetration testing agent (XBOW).
Critical Vulnerabilities to Prioritize
Microsoft Office & Excel
As is often the case, the most immediate risk to end-users lies in Microsoft Office. Two critical Remote Code Execution vulnerabilities, CVE-2026-26110 and CVE-2026-26113, can be triggered simply by viewing a malicious email or file in the Preview Pane.
Additionally, CVE-2026-26144 is a critical information disclosure flaw in Excel. In a corporate environment where Excel files often house sensitive financial data, this cross-site scripting (XSS) vulnerability could allow attackers to exfiltrate data silently.
SQL Server Elevation of Privilege
CVE-2026-21262 is a publicly disclosed flaw that allows an authorized attacker to elevate their privileges to sysadmin over a network. While it requires low-level privileges to start, the leap to sysadmin makes this a top priority for any organization running SQL Server 2016 or later.
Key Takeaway: Even without active "in-the-wild" exploitation reported yet, the public disclosure of these flaws means the "clock is ticking" for defenders to apply patches before exploit code becomes widely available.
Publicly Disclosed Zero-Days
Two vulnerabilities were known to the public before a patch was available this month:
CVE-2026-21262: The SQL Server elevation flaw mentioned above.
CVE-2026-26127: A Denial of Service (DoS) vulnerability affecting applications running on .NET 9.0 and 10.0.
Official Microsoft Resources & Downloads
To secure your environment, refer to the official documentation and update catalogs provided by Microsoft:
Official Summary: Microsoft Security Update Guide (March 2026)
Windows 11 Hotpatch: KB5079420 Release Notes
SQL Server Update: KB5077465 (SQL Server 2022)
Office 2016 Update: KB5002838 Security Update
While the lack of exploited zero-days is a welcome relief compared to last month, the high volume of privilege escalation bugs and the "Preview Pane" risks in Office mean that "business as usual" patching isn't enough. Organizations should prioritize their SQL Server and Office deployments immediately.
Are your systems up to date?
Check your Windows Update settings or your WSUS/Intune consoles to ensure these critical fixes are being deployed.
Did you enjoy CarlsCloud™ today and did I help you at all?
If so, buy me a coffee or just shoot me a note via LinkedIn to say thanks it would mean a lot!